Certifications & Security

RGPD certification issued in accordance with article 42 of the RGPD
The regulation nᵒ 2016/679, known as the General Data Protection Regulation (GDPR), is a text that aims to protect users’ personal data, i.e. any information relating to an identified or identifiable person, directly or indirectly, from a single data or by cross-referencing a set of data.
The GDPR governs the processing of personal data and stardardizes the rules in the European Union by providing a single legal framework for all professionals who can develop their digital activities on the basis of user confidence.
This certification is based on a standard developed and maintained by the European Centre for Certification and Privacy Protection (ECCP, http://eccpcenter.org) and approved by the European Data Protection Committee (EDPS, https://www.edpb.europa.eu/), an independent European body bringing together the heads of national supervisory authorities (the CNIL in France).
As a result, Europrivacy certification is officially recognized by the data protection authorities of 30 countries: all EU and EEA member states.
By committing to this voluntary process provided for in Article 42 of the RGPD, CASD continues to demonstrate its acquired ability to integrate high standards of data protection into its hosting and data processing infrastructures. This illustrates the ongoing alignment between its technological choices and European regulatory expectations.
The certification was issued by TAM-CERT, an independent, accredited certification body specializing in data security and protection, which conducted an exhaustive audit of CASD according to the methodology prescribed by Europrivacy to assess, document, certify and enhance compliance with the European General Data Protection Regulation.
Certificate number: 00A6:A057:A01E:0011
The security at the core of CASD know-how
Granting access to confidential data is of the utmost importance for studies and research. Detailed personal data require a high level of security to avoid unwarranted dissemination or misuse (by an unauthorized third party) and, therefore, makes infrastructures, tools and systems allowing access critical.
To address these issues, CASD has put together its set of technologies for data dissemination which guarantees security and technically prevents any data file export.
CASD used all its know-how to create a secure data hosting setup compliant with the French regulation pertaining to the processing and dissemination of data protected by secrecy.
The party wishing to disseminate its confidential data can :
- Have their data hosted at CASD;
- Name the authorized persons to access the data (for the amount of time the party will have chosen);
- Instruct CASD as to who will be authorized to have an SD-box;
- Define the confidentiality rules.
This is in order to benefit from the guarantee of high level security for their data through confinement to avoid dissemination, while maximizing user comfort in terms of ergonomics and IT efficiency.
CASD processing has been authorized by the Commission Nationale de l’Informatique et des Libertés, CNIL (CNIL – Delibération number 2014-369).
ISO 27701 – Privacy information management system
The international standard ISO 27701, GDPR compliant, is an effective reference to take into account the best practices in the field of personal data protection. It complements the international standard ISO 27001 and aims to provide a framework for the protection of personal data with both a technical and organisational approach.
This standard was developed with the help of numerous data protection authorities, including in particular the CNIL : l’ISO 27701, une norme internationale pour la protection des données personnelles.
The CASD hosts personal data from several major institutions and it is essential that the CASD can provide strong guarantees for the protection of this data. With increased compliance, users benefit from the potential for more data for research and study purposes.
Certificate number : 2025/114655.2
ISO 27001 – Information Security Management
ISO 27001, the international standard in the field of IT security, covers all legal, physical and technical controls involved in an organization’s information risk management.
By adopting an Information Security Management System (ISMS) and being ISO 27001 certified, CASD reinforces its ability to :
- Protect data against disclosure, loss, theft, alteration, intrusion ;
- Ensure business continuity ;
- Identify and control the risks of IT failure ;
- Take risk management decisions based on the CASD’s strategic objectives and ensure a high level of information security ;
- Guarantee users a robust ISMS and the reliability of its information system.
This certification covers the scope concerning the provision of secure services (or “secure bubbles”) for data hosting infrastructure via biometric access controls and encrypted connection from a dedicated box (SD-Box) installed in establishments that have signed a contract with CASD.
CASD management and all CASD employees, most of whom are themselves certified « ISO 27001 Lead Implementers », actively contribute to the safety process by implementing and respecting the technical, procedural and organisational safety measures that implement the CASD safety guidelines. To this end, the ISMS is monitored, reassessed and improved every year and all stakeholders in this process are regularly trained and made aware of the challenges and new threats related to information security.
Certificate number : 2025/114647.2
HDS – Health Data Hosting
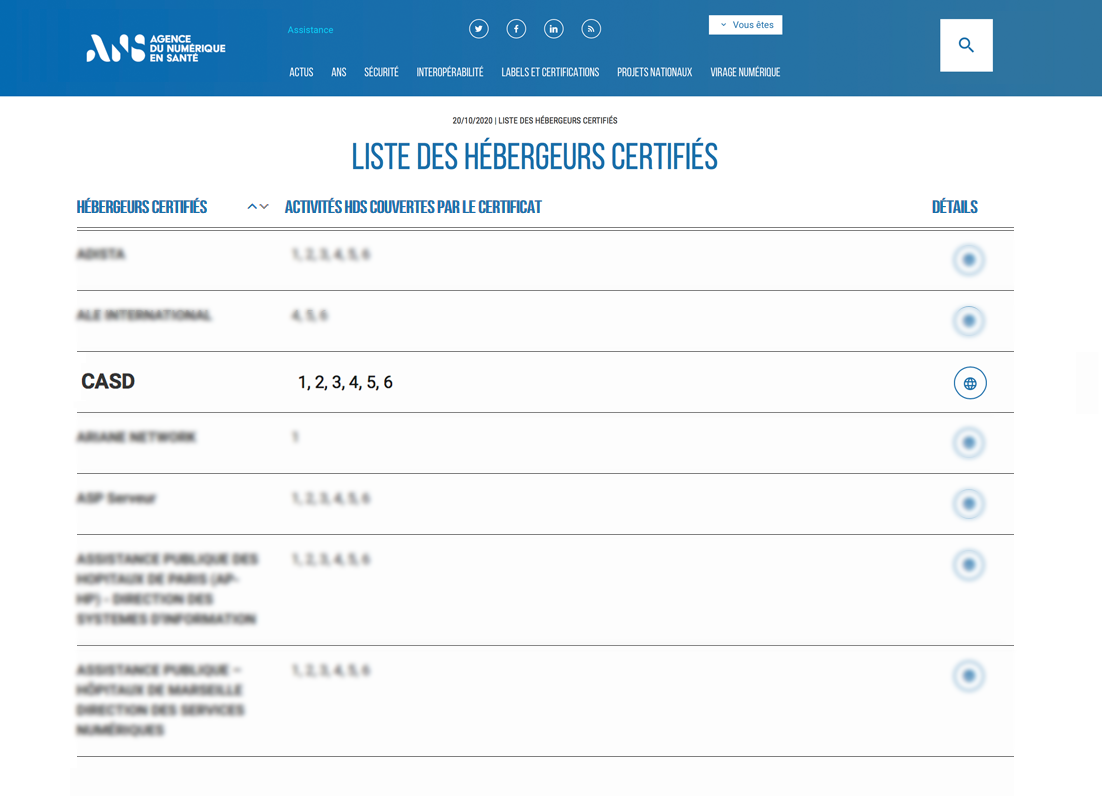
In addition to ISO 27001 certification, CASD has obtained the « Hébergeur de Données de Santé » (HDS – Health Data Hosting) certification from ASIP Santé, thus widening the scope of health data made available on the CASD.
Launched on April 1, 2018, the HDS certification attests of CASD’s ability to securely host personal health data collected during prevention, diagnosis, care or social and medico-social follow-up activities.
The CASD implements a management system adapted to their criticality to protect this sensitive data but also to secure all information and prevent the risks of malicious intent and cyber attacks.
With this certification, CASD guarantees the protection of personal health data and promotes a trusted environment around e-health and patient follow-up.
Certificate number : 2025/114648.2
Certification to the Health Data Security Standard (SNDS)
The decree of 22 March 2017 relating to the safety standard applicable to the National Health Data System (SNDS) sets out constraints for the provision of SNDS data.
Indeed, the data made available in the SNDS is sensitive. Although stored on the basis of pseudonyms, the combination of several variables can lead to the identification of the citizens concerned, which constitutes a risk of invasion of privacy. The standard was developed on the basis of a rigorous risk analysis in order to put in place the appropriate security measures.
Access to data is provided under conditions ensuring the confidentiality and integrity of the data and the traceability of access and other processing, in accordance with a reference system defined by decree of the ministers responsible for health, social security and digital technology, adopted after consulting the « Commission Nationale de l’Informatique et des Libertés » (CNIL).
Here is the table describing CASD’s compliance with the SNDS:
| SNDS | CASD | |
|---|---|---|
| Risk analysis | Carried out exhaustively for “medical files”. | |
| Impact study | Idem Risk Analysis | |
| Carrying it out | Completed | |
| Testing | Completed | |
| Labelling | To be done with the person in charge of processing | |
| IT monitoring and follow up | Completed | |
| Externalisation | ||
| Risk Analysis | Completed, Detailed risk analysis | |
| PGSSI | OK | |
| Audit modalities | OK – synthesis can be supplied on demand | |
| Export | OK – only towards RSDS | |
| Awareness raising | OK – enrolment sessions and contracts awareness raising and training for administrators |
|
| Access modalities | ||
| Availability | 24/24, 7/7 | |
| Access from an internal work station (PSSI-MCAS) | Dedicated SD-Box™ The SD-Box™ has a dedicated use that is subjected to a high level of security |
|
| Data output | Verification of a priori or a posteriori outputs with traceability and accountability (integrity by encryption) Code of Good Practice of European Statistics |
|
| Data integrity | The user only has reader access to source data (no editing or other type of access authorized). | |
| Admin access | Users and administrators have no internet access. SD-Box™ guarantees the Bubble’s isolation |
|
| Identification and authentification | ||
| Identification | Physical identification | |
| Authentification | Certification, access card, biometry, Authorization number 2014-369 by the French authorities (CNIL) | |
| Traceability | ||
| Authentification | Strong Certification, access card, biometry |
|
| Role and authorization management | OK, centralized by a directory | |
| User Referential | OK – Secure dedicated software | |
| Resource referential | OK – Secure dedicated software | |
| Role and authorization referential | OK – Secure dedicated and synchronized software | |
| Shared dating | OK – Dedicated infrastructure | |
| Tracing back | OK, session record | |
| Specific Documentation | OK | |
| Trace logs: access, outputs, data matching, and admin operations. | OK, technical traces The need to trace can be arbitrated upon according to the risk |
|
| Surveillance | ||
| System response time | OK | |
| Increasing rights; | OK – Audited regularly | |
| Non-authorized output; | OK – Audited regularly and tracebility | |
| Non-authorized access to SNDS resource; | OK – Audited regularly | |
| Unusual modification source data from the SNDS; | OK – Reading only | |
| Too large output | OK – Audited regularly | |
| Incident handling | OK – See “palier 3 imputabilité” | |
| Time-stamping | OK – Dedicated and recorded procedure | |
| Regular audits réguliers | OK – At minimum, annually | |
| Authorisation review | OK – At minimum, annually | |
| Access rights | If possible technically (excluding anonymisation) | |
The purpose of these certifications is to provide formalized guarantees to data producers, rightly concerned that the use of data should be carried out in a framework that provides appropriate security for confidential data.
Audits
Auditing companies aim to verify as completely as possible the level of security cleared by CASD infrastructure within the constraints defined by data depositors.
The auditor must be specialized in IT security, PASSI (IT audit label) and labelled by the ANSSI (national agency for IT security), as well as competent in client OS, server, VPN attack methods, authentification mode attack methods, etc.
Audits follow 4 gradual scenarios which aim to successfully intrude, usurp identity, or retrieve a data file.
SCENARIO 1 : Internet encrypted tunnel attack with no declared IP public address
The auditing company knows the CASD network address, but the IP address is not among the list of addresses authorized to connect to CASD.
The company must study if an attack is possible on the VPN-SSL tunnel outlet, or if it is possible to extract information from this tunnel.
SCENARIO 2 : Internet encrypted tunnel attack with a declared IP public address
The company knows the CASD network address, the IP address is within the list of addresses authorized to connect to CASD.
The company must study if an attack is possible on the VPN-SSL tunnel outlet, or if it is possible to extract information from this tunnel.
SCENARIO 3 : Internet encrypted tunnel attack with a declared IP public address and in possession of an SD-Box
The company knows the CASD network address, the IP address is within the list of addresses authorized to connect to CASD, and they are in possession of an SD-Box.
The company must study if an attack is possible on the VPN-SSL tunnel outlet, or if it is possible to extract information from this tunnel.
The auditor will test if they can take control of the box:
– Take control of the OS (modification of the boot),
– Access the Shell one way or another,
– Access the RDP to open a session remotely,
– Access the box through the network,
– Usurp the central infrastructure (attack of the “man in the middle” type),
– Access USB ports, boot on a USB port,
– Modify the Bios,
– Read the hard-drive content (and if so try to connect),
etc.
This list is non-exhaustive and the company must attempt a maximum number of attacks (known or unknown to CASD) in that configuration.
SCENARIO 4 : VPN-SSL Internet attack with a declared IP public address, a smartcard and in a possession of an SD-Box
The company knows the CASD network address, the IP address is within the list of addresses authorized to connect to CASD, and they are in possession of an SD-box and a smartcard.
This attack configuration mimics an internal intrusion attempt. The company can connect as an internal user would. An account will be created specifically for this testing purpose.
The aim is to launch hijacking maneuvers to address at least one of the following issues:
– Is it possible to retrieve a file?
– Is it possible to access files to which the user has theoretically no access to (files or other projects)?
– Is it possible to usurp a user’s identity with or without his card?
Resilience tests to authentification modes will also be done (card tests, driver tests, etc).
Audit report
It must be complete and specific regarding the testing modalities, protocols used, source codes for the programs used in the attacks…
4 audits were carried out successfully by companies certified by the ANSSI.
PGP
CASD’s Public PGP key can be used to secure data before sending it to CASD. You can contact us at service@casd.eu for further information.
TÉLÉCHARGER LA CLEF PGP PUBLIQUE DU CAS
Download casd’S PGP key
Details on the key :
ID: 2BBE1271
Type : RSA
Size : 4096/4096
Created : 2013-06-12
Expiration : None
Cipher : AES-256
Fingerprint : 53B8 8ED6 A9F1 0E0B 62FD 5208 889E 5557 2BBE 1271